Why This Standard Exists
Most SOC stacks duplicate investigation logic across SIEM, SOAR, and custom playbooks. Tool-specific branching semantics make cross-platform verification difficult.
Open Standard For Security Investigation Logic
Use stable node and edge semantics, run the shared conformance suite, and contribute improvements without forking core behavior.
Most SOC stacks duplicate investigation logic across SIEM, SOAR, and custom playbooks. Tool-specific branching semantics make cross-platform verification difficult.
AI-assisted workflows can drift when branch rules are implied in prompts instead of encoded in deterministic graph transitions.
TENSOR keeps investigation intent stable while allowing implementation details to vary by vendor and organization.
Node and edge identifiers remain portable across releases, enabling replay, diffing, and migration checks.
Every transition resolves to yes, no, or unknown, so execution rules are testable.
Teams can layer local business logic without mutating core investigative semantics.
Baseline fixtures and release telemetry provide objective signals for implementation readiness.
Adoption is incremental. Implement the level that matches your product role, then move upward as your integration matures.
| Level | What You Support | Pass Criteria |
|---|---|---|
| Consumer | Load and validate canonical graph + schema artifacts. | Accept valid fixtures and reject invalid fixtures with deterministic errors. |
| Executor | Traverse decisions using graph semantics in runtime workflows. | Produce reproducible branch transitions and audit records for traversals. |
| Authoring Tool | Create or modify graphs while preserving compatibility policy. | Emit schema-valid artifacts and maintain stable IDs across revisions. |
yes/no/unknown transitions.Loading live framework metrics…
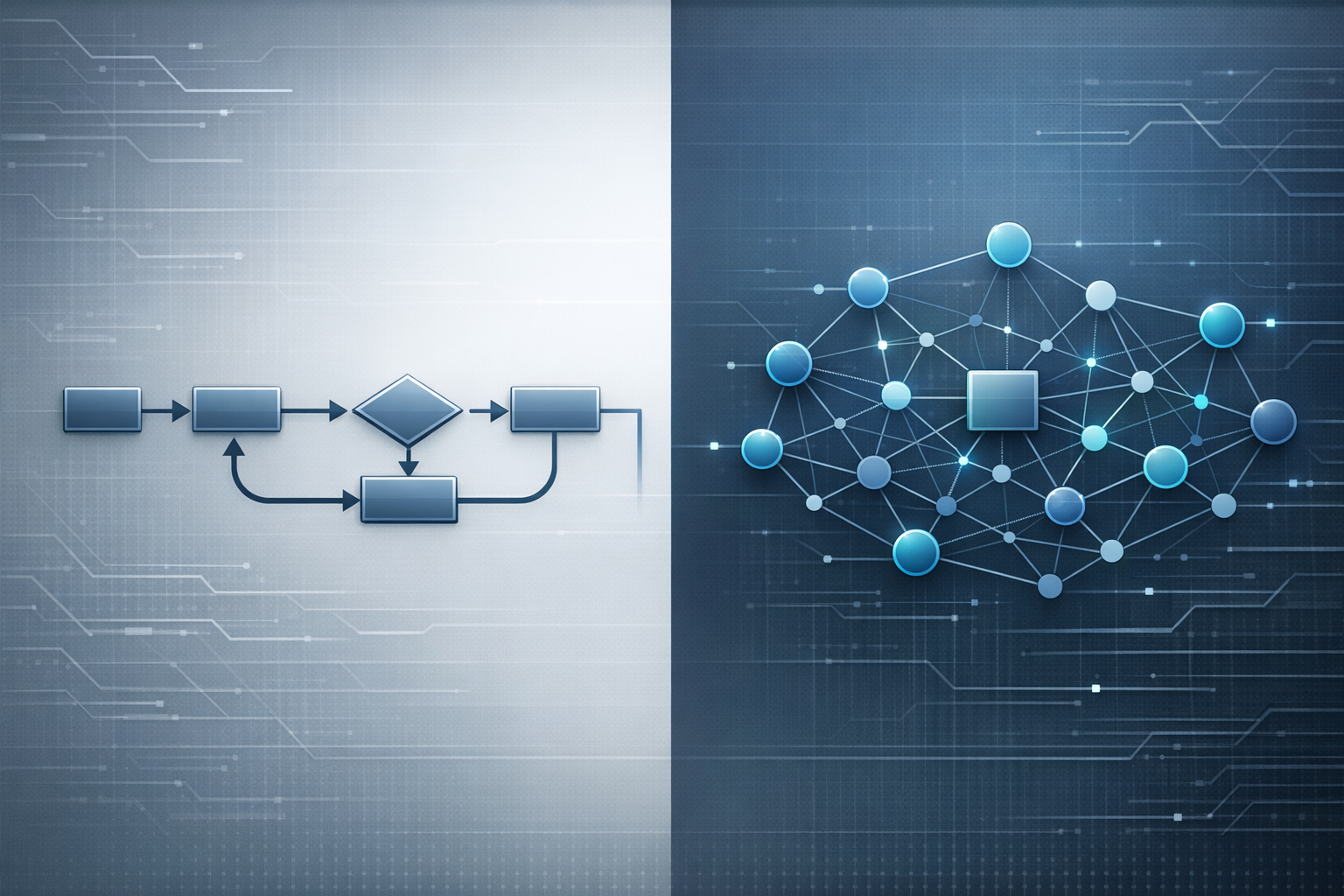
Investigation Model Shift
Traditional workflows are usually linear with optional loop-backs. TENSOR preserves those patterns, but encodes reusable logic once so integrators can apply the same semantics across platforms.
Next step: review standards and compatibility policy before implementation.